Theme Security
NEVER TRUST USER INPUT
There are two main keywords you must keep in mind when considering security for input.
- Validation
- Sanitization
VALIDATION
Validation refers to the checking of data, if it meets certain datatype or certain data formats, for example, if the email looks like an email ( it won’t be a good thing if someone passes url as email 😛 )
The validation checks and return if the data is correct, -> there data is either accepted or rejected.
SANITIZATION
Sanitization refers to the cleaning of data, or we can say removing illegal characters from the data. For example, if someone sends [email protected] as the URL and we want to sanitize the url the out result must be google.com the illegal character @ must be removed from it.
The sanitization removes illegal characters from the data.
Sanitization is a very important aspect as the end user can send malicious code which can get executed with the scripts to cause damage to the data. for example SQL Injections.
There’s also a third term -> ESCAPING
ESCAPING
Escaping refers to the conversion of illegal character to some non-hurting values. For example, converting <script> to
<script>This would look as the same in the html -> But executes very differently 😀
The first one would get executed as the javascript code and can be used to execute malicous content.
WordPress support for escaping
WordPress have many built in functions to make the escaping pretty easier.
- esc_html()
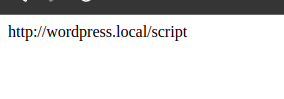
This function is used to escape html content. - esc_url()
This function is used to escape urls.
echo esc_url( 'http://wordpress.local/<script>' );This would give us the escaped url
- esc_js()
This function is used to escape inline JS content - esc_attr()
This function is used to escape the data for the HTML attributes.
echo esc_attr( 'data<script>window.href="https://www.google.com";</script>' );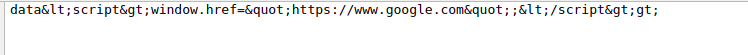
- esc_textarea()
Escaped the data to be used inside a textarea
echo esc_textarea( 'something"' );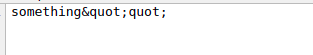
- wp_kses()
This function is used to sanitize the html content to be displayed, the second parameter is sent as the array of allowed html tags
Some sanitization functions which wordpress provides are
- sanitize_textarea_field()
- sanitize_hex_color()
- sanitize_title()
- sanitize_title_for_query()
- sanitize_key()
- sanitize_file_name()
- sanitize_meta()
- sanitize_title_with_dashes()
- sanitize_user()
- sanitize_hex_color_no_hash()
- sanitize_email()
- sanitize_html_class()
- sanitize_mime_type()
- sanitize_url()
- wp_kses()
- wp_kses_post()
- sanitize_option()
- sanitize_sql_orderby()
- sanitize_text_field()
